EC Orlando '24 is a Wrap!
Announcing: Enterprise Connect AI - October, Santa Clara, CA
Enterprise Connect AI - Optimizing AI for Enterprise Growth
A Two-Day Summit For Enterprise IT, Communications and CX Leaders
We are excited to announce a new event taking place October 1-2, 2024 in Santa Clara, CA: Enterprise Connect AI.
With AI moving at a frenetic pace and IT leaders scrambling to keep up, this new 2-day event will provide up-to-the-minute, in-depth, unbiased content with conference tracks covering CX, Productivity, and IT Management to help the Enterprise IT community leverage AI to advance the enterprise.
Dive into critical AI topics with 3 Conference tracks:
- CX: Learn how AI is transforming CX for the customer, the contact center agent and the business
- Productivity: Discover how to ensure end users are getting the promised benefits and safely exploring new ways to build on success, with tools ranging from meeting summaries to “co-pilots” for everything from sales to finance to coding, plus applications for improving business processes
- IT Management: Find out how AI can make teams more efficient & effective and help find ways to save money or make money for the business
Want to share your wealth of knowledge at the Enterprise Connect AI event? Click this link to get more info on the Call for Speakers program and submit a proposal.
Resources for an AI-driven Future
AI, CX and Personalization: Is the Time Right?
From personalized recommendations to predictive customer service, AI revolutionizes CX. However, challenges such as data accuracy, bias, and customer confidence remain. This report guides you on how to leverage AI for unparalleled personalization. Whether you're at the forefront of AI adoption or just beginning the journey, this is your roadmap to staying ahead in 2024 and beyond.
The LLM Conundrum: What Does GenAI Really Cost Your Company?
With hundreds of millions of people using Large Language Models (LLMs), also called Generative AI (GenAI), to answer queries, write poetry, pass the Turing test and so much more, it’s safe to say that each one has a pretty good idea what using an LLM costs. This report will provide you with an understanding of the cost-drivers that give shape to pricing regimens of foundation LLM providers.
Industry-Leading Keynotes
Expert leaders from Cisco, Microsoft, RingCentral, and Zoom will take the stage to address the most critical issues facing the enterprise IT industry today.
Generative AI, AI in the Contact Center and More Hot Topics
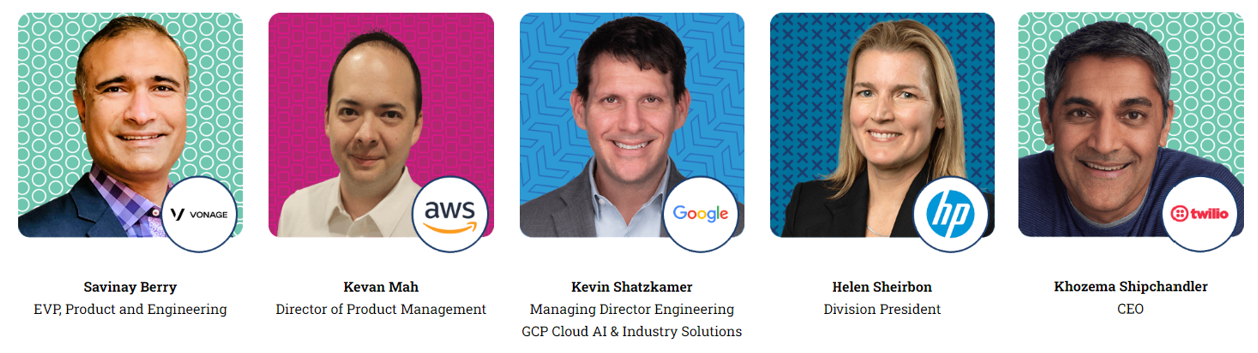
Google, AWS, Vonage, HP & Twilio lead our Keynote Fireside Chats - insightful 15-minute discussions with industry leaders on topics including:
Employee Experience • Generative AI • Customer Engagement • AI in the Contact Center
Hear From IT Pros Across Different Industries
Our 2024 Conference Program features more enterprise speakers than ever before! Gain insight into real-world experiences in sessions led by enterprise IT peers facing the same challenges as you!
AI-Driven Future for Communications, Collaboration and CX
Enterprise Connect focuses on today's newest technologies to keep you at the forefront of the enterprise IT industry.
Featuring 10 conference tracks and 15+ end-user-led sessions, Enterprise Connect covers all the hot topics you want to hear about, including Generative AI, CX, EX, UC, video meetings, and more.
With AI permeating so many aspects of IT/comms technology, you have to keep up with the principles, impacts — and risks — behind this revolution. But it’s not just about AI in products; the opportunity to benefit by automating IT processes has never been greater. Master the concepts and opportunities in AI and automation at Enterprise Connect. Sessions include:
- Is Gen AI Already Delivering Business Value to Enterprise CX?
- Navigating the LLM Landscape: Understanding and Leveraging AI-Powered Features
- Reality Check: How Not to Fall Behind in AI
- Focus on Automation Ahead of AI
With over 5,000 IT, CX, and Communications professionals in attendance, you'll have plenty of opportunities to network and make connections with peers facing similar challenges.
Expo Hall – Source Solutions From 150+ Exhibitors
"Great speakers, exhibitors, and a great buzz on the expo floor." - 2023 Attendee
Enterprise Connect is the BEST place to source products and services from competing system and software vendors. Featuring the largest Expo Hall for communications and CX professionals in North America, you can meet with designers and developers of systems for unified communications, contact centers, video, collaboration platforms, and much more.
Experience the energy and excitement of our show floor while exploring new solutions.
- Attend interactive panel discussions
- Connect with peers during networking receptions and happy hours
- Check out product demonstrations and have face-to-face meetings
- Compare 150+ solution providers side-by-side
- Win gift cards and consumer tech goods via our Passport-to-Prizes program
NEW: Half-Day Training Courses
Half-Day Training courses, presented by leading industry experts, are designed to help decision-makers get a grounding in the key issues and a solid foundation to move forward as these critical topics continue to grow in importance within your enterprise.
Select from training courses on the following topics:
2024 Conference Sessions & Tracks
Our expert-led conference program will hone in on the latest systems, software, services, and applications for enterprise communications and collaboration. Our ten conference tracks cover the full scope of issues impacting Enterprise IT professionals today and into the future. Whether your focus is on Employee Experience, Data Analytics, A/V or Security & Compliance, there is something that will help your organization.